In today’s digital world, protecting your data and systems from cyberattacks is more crucial than ever. And one of the most effective ways to do this is through a process called threat modeling. Think of it as building a security blueprint for your home—you identify potential vulnerabilities and create countermeasures before burglars even try to break in.
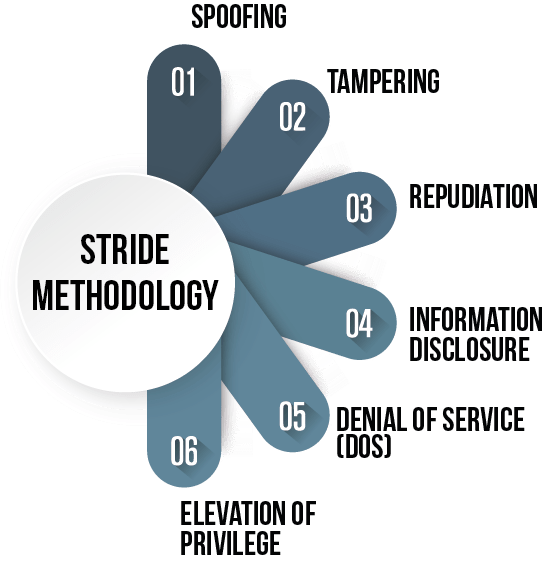
STRIDE is a popular and well-respected threat modeling framework that can help you do just that. It’s designed to uncover security threats early in the development process, making it easier and less costly to address them.
Here’s a breakdown of how STRIDE works:
- Identifying Assets: What are the critical components of your system that need protection? Data, software, hardware, and network components are all examples.
- Defining Threats: STRIDE uses six categories to classify threats:
- Spoofing: Pretending to be someone else to gain access.
- Tampering: Modifying data or code without authorization.
- Repudiation: Denying actions or events.
- Information Disclosure: Exposing confidential information.
- Denial of Service: Making a system unavailable to users.
- Elevation of Privilege: Gaining unauthorized access to resources.
- Analyzing Vulnerabilities: Pinpointing weaknesses in your system that could be exploited by threats.
- Prioritizing Risks: Determining which threats pose the most significant risks and need immediate attention.
- Implementing Countermeasures: Taking actions to mitigate risks and protect your assets, such as using encryption, access controls, and regular security audits.
Types of Threat Modeling
- Some of the common types of threat modelling are asset-centric, attacker-centric, software-centric, and hybrid.
- STRIDE belongs to the software-centric type, as it focuses on the design and implementation of the system or application, rather than the assets or attackers.
5 Steps in Threat Modeling
- Decompose the Application: Create a model of the system or application, such as a data flow diagram, that shows the components, data stores, data flows, and trust boundaries.
- Identify Threats: Use the STRIDE model to find potential threats for each element and interaction in the model, such as asking questions like “Can an attacker spoof this user?” or “Can an attacker tamper with this data?”.
- Analyze Threats: Assess the severity and likelihood of each threat, using criteria such as damage, reproducibility, exploitability, affected users, and discoverability.
- Mitigate Threats: Propose and implement countermeasures for each threat, such as encryption, authentication, logging, or firewall.
- Validate Threats: Review and test the effectiveness of the countermeasures, such as using tools, techniques, or metrics to verify that the threats have been reduced or eliminated.
How is STRIDE Framework applied to improve organisation security posture?
STRIDE framework can help organizations improve their security posture, such as by:
- Providing a structured and systematic approach to identify and mitigate threats, rather than relying on ad hoc or reactive methods.
- Enhancing the security awareness and culture of the organization, by involving stakeholders from different roles and perspectives, such as developers, testers, managers, and users.
- Improving the security quality and maturity of the system or application, by integrating security into the design and development phases, rather than adding it as an afterthought or a patch.
- Reducing the security risks and costs of the system or application, by preventing or minimizing the impact of potential attacks, rather than dealing with the consequences or damages.
Recommended approach to conducting STRIDE Threat Modeling
- Start threat modeling early and iteratively, as soon as the system or application is defined and throughout the development lifecycle, rather than waiting until the end or doing it once.
- Use tools and templates to support and automate the threat modeling process, such as Microsoft Threat Modeling Tool, OWASP Threat Dragon, or STRIDE Cheat Sheet, rather than doing it manually or from scratch.
- Collaborate and communicate with the relevant stakeholders, such as developers, testers, managers, and users, to ensure that the threat model is accurate, comprehensive, and aligned with the business objectives and requirements, rather than working in isolation or silos.
- Review and update the threat model regularly, as the system or application evolves or new threats emerge, to ensure that the threat model is current, relevant, and effective, rather than leaving it outdated or obsolete.
The benefits of using STRIDE include:
- Proactive Security: Identifying and addressing threats before they cause damage.
- Cost-Effectiveness: Fixing vulnerabilities early is often less expensive than dealing with breaches later.
- Improved Security Awareness: Encouraging a security-focused mindset throughout the development process.
STRIDE is a valuable tool for organizations of all sizes and industries. Whether you’re developing a new application, managing an existing system, or simply want to enhance your overall security posture, STRIDE can help you stay ahead of the curve and protect your valuable assets.

























